Blockchain Security 101: How the Average Person Can Build a Cryptocurrency Fort Blockchain technology has brought about a new era of innovation, dec
The topic of this article is security in the crypto world, specifically how to build a firewall around your assets to invest in a secure environment, which is a prerequisite before we embark on our crypto journey.
Original Article Title: "EP28: How Much Do You Know About On-Chain Security: How Ordinary People Can Build a Cryptocurrency Firewall"
Original Source: Mint Ventures
· Host: Alex, Research Partner at Mint Ventures
· Guest: Zhou Yajin, CEO of the blockchain security company BlockSec
· Recording Date: March 28, 2025
Disclaimer: The content discussed in this podcast does not represent the views of the guests' respective organizations, and the projects mentioned do not constitute any investment advice.
Hello, welcome to WEB3 Mint To Be initiated by Mint Ventures. Here, we continue to question and think deeply, clarify facts, uncover realities, and seek consensus in the WEB3 world. We aim to clarify the logic behind the hot topics, provide insights beyond the events themselves, and introduce diverse perspectives.
BlockSec's Service Scope and Target Clients
Alex: In this episode, we will discuss a topic that is closely related to all of you, which is security in the crypto world. It's often assumed that we will not become the victims of security incidents in the news until we actually face real risks. How to build a firewall for your assets, allowing yourself to invest in a secure environment, is a prerequisite for starting our crypto journey.
In this episode, we have invited Zhou Yajin, CEO of the blockchain security company BlockSec, to talk to us about the topic of crypto security. Let's have Mr. Zhou greet us.
Zhou Yajin: Hello, I am Zhou Yajin, currently the CEO at BlockSec. I am also a researcher in cyberspace security at Zhejiang University. It's a pleasure to meet everyone.
Alex: Alright, let's get into today's topic. I believe many listeners may not have a deep understanding of blockchain security companies and security services. Could Mr. Zhou first introduce BlockSec to us, the services you provide, and what kind of individuals and institutions would become your clients?
Zhou Yajin: Sure, BlockSec is a Web3 security company founded in 2021 by me and Professor Wu. When it comes to Web3 security, people may first think of security audits. In fact, BlockSec's business scope is not limited to security audits; we also provide a series of other security products and services. Specifically, our services can be divided into three major categories.
The first pillar we refer to as On-Chain Protocol Security. On-chain protocols are smart contracts deployed on the blockchain for activities such as DeFi or NFTs. How should the security of these contracts be ensured? BlockSec provides security audit services and secure monitoring products.
The second pillar we are particularly concerned about is Asset Security. Asset security refers to the assets held by users, whether in their own smart contract wallets or invested in on-chain protocols. Ensuring the security of these user assets is also within the scope of BlockSec's services.
The third pillar is Compliance and Regulation. We have seen an increasing number of traditional financial institutions entering the crypto industry. Recently, we have seen news of traditional U.S. banks issuing stablecoin assets on-chain and cryptocurrencies entering the cross-border payment industry. As these traditional financial institutions enter this industry, they pose a challenge to regulators who do not know how to regulate them, and these institutions do not know how to comply with regulations. Therefore, we also assist regulatory bodies in regulating players entering the crypto industry or help traditional institutions entering the crypto industry to achieve compliance. These are the three areas of our business.
Our client base is quite broad. Think of projects conducting decentralized finance or other services on-chain, such as lending platforms or decentralized exchange platforms — these project teams are our clients. We can help them conduct security audits before deploying smart contracts on-chain by reviewing their smart contracts from a security perspective for any vulnerabilities. If there are security vulnerabilities, they need to be fixed promptly. Additionally, once their protocol is deployed on-chain, we provide a 24/7 monitoring platform to monitor their protocol's security risks. If any security risks occur, our platform can promptly notify the protocol and automatically mitigate risks and attacks.
Therefore, developers and project teams deploying smart contracts on-chain are a typical type of client for us. The second typical type of client is asset holders, such as some high-net-worth individuals who hold assets in smart contract wallets or invest in on-chain protocols. Our services and products can help them better monitor the security of the protocols in which they have invested. Just like the two sides of a coin, from the perspective of the protocol project teams, we can help them enhance the security of their protocols.
From the perspective of high-net-worth clients investing in their protocol, we can help them monitor the security of the protocol they have invested in. Once the protocol they have invested in faces a security risk, such as an attack, they need to be able to withdraw their funds immediately. The third type of client is what I just mentioned about regulation and compliance. This type of client is mainly some regulatory bodies, such as the Securities and Futures Commission of Hong Kong, which is actually our client, and some overseas law enforcement agencies. When they need to investigate cryptocurrency-related crimes, they need to use our tools and platform to easily conduct activities such as evidence extraction and fund tracing. This basically represents our overall business and the range of our clients.
Three Points of Advice on Crypto Security
Alex: I see. Just now, Teacher Zhou talked about the types of clients, their needs, and an overview of the industry. The second question may be more relevant to individual investors, especially since many of our listeners are just starting to learn about Web3 and explore investment.
If you have a friend who has just entered the cryptocurrency investment field and knows that you provide cryptocurrency security services, please give him three pieces of advice on cryptocurrency security. What would be the three pieces of advice you would give him?
Yajin Zhou: This is a very good question. My friends around me often ask me for some security advice as they also want to enter this industry, but they have heard that many people seem to encounter some risks. We once had a joking saying: if you have not been phished or scammed after entering the Crypto circle, you will not become a seasoned player in this field. Of course, this is a joke, but indeed you can find many risks in this industry.
If I were to give three pieces of advice, the first piece of advice would definitely be something everyone would think of, which is about protecting your private key. In the Crypto field, how you prove that you own these funds is actually by using the private key you have to prove your ownership of the account. The private key is just a string of numbers, which is not tied to your personal identity at all. Once this string of numbers is lost or leaked, others can have the same control over your funds as you do. This is very different from the real world. In the real world, if your bank password is leaked, you can call the bank to freeze the account, and others cannot withdraw money. But in the Crypto world, if your private key is leaked, then the person who has your private key can freely transfer your funds out of your account.
Generally speaking, there are several ways to protect a private key. For example, we have hardware wallets, smart contract wallets, or mobile apps to safeguard the private key. Each method actually has its own pros and cons. Based on my own experience and the collective experience of some security-conscious friends around us, the fundamental principle is the mnemonic phrase of the private key. Write it down and store it in a safe, whether it's at your home or in a bank. Keep it secure, do not touch it regularly, as you probably won't need it often. Then, use a relatively trustworthy device, whether it's a hardware wallet or a mobile phone, to securely store your private key. This phone must be a dedicated device used solely to manage your digital assets. That's the first recommendation.
The second recommendation is to always be aware of security and risks when transacting on-chain. Essentially, just remember one thing: free cheese only in a mousetrap. We have found that during on-chain transactions, users face a significant phishing risk. Many well-known figures in the crypto community, including Key Opinion Leaders (KOL) and Original Gangsters (OG), have fallen victim to phishing attacks and lost substantial funds. If an unknown website asks you to connect your wallet to receive a so-called airdrop reward, you should be cautious and maintain a security-conscious mindset.
The third recommendation is to have a basic understanding of cryptocurrency fundamentals. By basic understanding, we refer to the concept of authorization commonly found in the world of cryptocurrencies. This concept sets crypto apart from traditional finance. For instance, if you own a particular type of digital asset like USDT or USDC, through on-chain signatures, you can authorize the use of the asset by a smart contract or another user. This authorization only requires your wallet to sign a bunch of gibberish that you may not comprehend.
Therefore, when signing wallet signatures, if you lack understanding or are deceived into signing an authorization transaction, others can access all your digital assets. Hence, you need to have a basic understanding of authorization to avoid mistakenly signing such transactions. In summary, the main recommendations are: first, safeguard your private key, with some actionable methods provided; second, exercise caution and maintain security awareness during on-chain transactions to avoid phishing attempts; third, have a basic understanding of the cryptocurrency authorization mechanism to prevent mistakenly signing authorization transactions.
Alex: I actually have many high-net-worth friends around me, who are also OGs or industry veterans. In theory, they should all have some level of security awareness you mentioned, but every year I hear about some whales around me being hacked.
There is a saying in the industry that if a professional hacker targets you and knows that your wallet is rich, if they utilize all available resources, you will likely have a hard time escaping. Do you think this saying makes sense? Is it really the case?
Zhou Yajin: Your question is very good. In fact, security issues, especially concerning Crypto security, are fundamentally an unbalanced confrontation. If your wallet holds a sufficient amount of assets, you become a prime target for a directed attack. Once you become the target of a directed attack, the attacker will utilize a significant amount of resources, whether social engineering, technical resources, or other resources, to design an attack tailored to you based on your daily behavior patterns, lifestyle habits, etc. In this scenario, it cannot be said to be 100% certain, but the difficulty of defending yourself is very high because the attacker has employed a considerable amount of resources against you, while you only have yourself. Therefore, it is a highly asymmetric confrontation.
Under these circumstances, I believe the basic principle is, firstly, we Chinese have a saying, "Do not flaunt wealth," which means you should not publicly disclose the assets you own and should avoid revealing the relationship between your offline identity and on-chain asset identity. Secondly, even if you are a high-net-worth user whose information may have already been leaked, you need to isolate your assets as much as possible. This means that the assets you normally operate with on a daily basis, in a dedicated wallet, might only amount to, say, 100,000 RMB, and if someone targets you, they can only scam that 100,000 RMB at most. Your other substantial assets should be kept in a wallet that is not used regularly. If you need to use these assets, you should seek a security professional to help you review a set of good operational procedures and standards, which can help mitigate significant risks.
Top Three Most Memorable Security Incidents
Alex: I understand, that advice is indeed very important. Could you share with us the top three security incidents that have left the most impression on you throughout your career? These could be incidents you personally experienced, incidents involving your friends, or incidents you have witnessed.
Zhou Yajin: I can share with everyone some security incidents that we were actually involved in handling and that have left a deep impression on us. The first example I remember was around mid-February 2023, when a protocol on the chain called the Platypus Protocol was attacked. It was a platform combining lending with other functionalities. This protocol had a security vulnerability, and through this vulnerability, the hacker managed to steal nearly 9 million USD worth of assets. The reason this incident left a deep impression on me was that the hacker made a mistake during the Platypus Protocol attack. When attacking the smart contract, they needed to develop a smart contract themselves. A smart contract can be understood as a self-executing piece of code. During the attack, the hacker deployed their own attack contract, and this contract completed the entire attack process.
However, the attacker is also human, and we all know that humans make mistakes. When he was writing the attack smart contract, he made a mistake, creating a vulnerability within the contract. This vulnerability allowed the funds stored in the attacking contract to be withdrawn, which were the funds obtained from the attack on the Platypus Protocol. As a security company, we are constantly monitoring on-chain attack events, and we have a set of attack detection engines that can quickly detect such attacks happening on-chain.
Coincidentally, when the Platypus was under attack, we had already detected it in real-time. We will independently analyze this security incident, including the reason for the attack and the location of the vulnerability. At the same time, we will also contact the project team to help them, informing them how to patch the vulnerability and how to handle the situation. During this process, we identified a vulnerability in the hacker's code and informed the project team that they could exploit this vulnerability. Then, together with the project team, we developed a piece of code to withdraw the attacked funds, specifically 2.4 million out of the 9.5 million taken by the attacker's contract. This marked the first time in blockchain security history that we referred to as a "hack back," meaning leveraging a vulnerability to extract the stolen funds and return them to the project team. It was a particularly interesting and memorable confrontation.
Alex: Did you have a cooperative relationship with Platypus before, or did you start communicating after this event?
Zhou Yajin: Actually, we did not have any prior cooperation with them. We only contacted them after this event. I can further explain the entire security incident response process. We have an in-house security attack engine, and when a security incident occurs, our engine will alert us immediately, and our internal emergency response team will analyze it together. First, we identify which protocol was attacked, and then through various means, whether on-chain, on Twitter, or other avenues, we will try to contact the project team.
In the case of Platypus, we didn't have their contact information beforehand. We reached out to the project team via Twitter and assisted them in analyzing the reasons for the attack because often project teams don't know why they were attacked; they just know that the funds in the protocol are gone, but the reasons are unclear. This is when a security company needs to step in to help with the analysis. Once the analysis is done, it involves how to repair the protocol.
If the reasons are understood, then the vulnerability needs to be patched, ensuring it is secure after patching, and tracking the stolen funds also require the assistance of security companies like us. We will continue to work with the project team throughout the entire emergency response process. In this specific case, we actually had no prior contact with this project, but fortunately, during the handling process, we were able to contact them in time and recover a portion of the funds. In many cases, we discover attacks but are unable to contact the project team.
Then the second case is also quite interesting, and this happened in 2023 as well. Our Chinese audience might be more familiar with this one because it involves a project called ParaSpace. ParaSpace is a protocol that allows staking of Bored Ape Yacht Club NFTs to borrow other assets. I know many Chinese OGs are actually holders of Bored Ape Yacht Club NFTs. This protocol actually had a security vulnerability and was attacked in March 2023. I distinctly remember it was around morning or noon Beijing time. Our system immediately alerted us,
First, we contacted the project team to analyze the root cause. However, we found that the first attack transaction our system flagged was reverted on-chain. Reverting means that the attacker did not include enough gas fees during the attack, causing the transaction to fail to be included in the block. However, the behavior of the attack transaction and its trace were still visible on the chain. Our system is also able to detect such transactions that we call reverse transactions, meaning they failed but still got confirmed on-chain. This is the capability of our engine to identify such attack transactions.
Once identified, we came up with a solution. We thought about whether we could simulate the behavior of the attack transaction, automatically generate a similar attack transaction, but with a twist. We would replace the address that profited in the transaction with our own address. Through this method, we could rescue the funds in the currently vulnerable protocol and transfer them to our secure account, then contact the project team to return the funds to them. This is akin to saying the bad actor's knife was about to strike, but for some reason, the first attempt was unsuccessful. We could also attempt to pre-emptively withdraw the funds using the same method so that when the attacker tried again, there would be no funds left in the protocol, causing the attack to fail.
Once we had this idea, internally, we had a system in place that allowed us to quickly automate such actions. We automatically generated a "fake attack" transaction, sent it to the chain, withdrew the $5 million worth of assets within the ParaSpace protocol, and then contacted the project team to return the funds. This was also very interesting; it was the largest rescue operation in history, where we rescued on-chain funds. Without this rescue, their assets could have been completely drained.
However, after this security incident, it also triggered a lot of contemplation for us because there were many security, moral, and ethical issues involved. For instance, after observing an attack and withdrawing the funds from the protocol, it is essentially still a transaction resulting from an attack. While simulating the attacker's behavior was done with good intentions to withdraw the funds and return them to the project team, strictly speaking, it was still an attack. This raises issues related to compliance and security ethics.
Our thinking at that time was, when you see a bad actor using a knife to stab a good actor, should you intervene or let it unfold. I think we chose to intervene, although there are some moral and security ethical issues involved. After this incident, we also deeply realized that on-chain security cannot be saved through the hack back we just talked about, which is hacking it back to save the funds. The project team should be informed of the security risk they are facing as soon as possible, knowing that the project is under attack, and then they can set up some automated running strategies.
When these security events occur, our system informs them that they should be able to automatically pause the protocol, so the attack will not succeed. By preventing the attack, saving users' funds, and avoiding any security ethical risks, we developed the idea behind the Phalcon attack monitoring and blocking products after these two incidents. This is the second major security event in my memory.
Alex: I think I also noticed this security event at that time. You just mentioned protective attacks. I want to ask a detail, which is after the revert attack occurred, you definitely needed an internal discussion and decision to see if a protective attack should be carried out. How much time elapsed between discovering this event and making the decision to protect the funds?
Zhou Yajin: Very quickly, from the moment we knew about it to the final completion of the matter, it was probably only a few minutes. Because the company has established a very sound security processing process, as soon as a security incident occurs, discussions and decisions will be made immediately, and because there are some automated tools already in place, things can be done quickly.
Alex: Understood.
Zhou Yajin: The third case is the recent Bybit security incident that everyone should have been paying attention to, where $1.5 billion in assets were stolen in February. This attack is also the largest single security incident in terms of losses in the security community to date, and its losses are very different from the two security incidents I mentioned earlier. The first two security incidents were caused by contract vulnerabilities, but Bybit's security incident has no relationship with smart contract vulnerabilities; we call it a long trust chain. In a system with such a large amount of funds and such a long trust chain, the attacker used a social engineering attack to find the weakest link and then carried out the attack. Specifically, Bybit used a contract wallet called SAFE, which is a smart contract wallet to manage its funds.
SAFE is a multi-signature wallet, which you can think of as a lock that requires three people to open simultaneously in order to access the funds inside. This lock is created by a project that provides such a smart contract wallet. You will find that in this system, the trust chain is very long, including the developers of the SAFE wallet, the individuals operating the SAFE protocol, the UI interface within the browser when using the SAFE wallet, and the operator of the SAFE wallet, which is the employee of Bybit holding three keys or the person with fund operation permission, who must operate this SAFE wallet through a computer's browser or a hardware wallet. You will find that many different aspects are involved in this process.
When we talk about security, the most challenging aspect of security in terms of attack and defense is that, during defense, you must ensure that your system has no weak points, as the security level of a system depends on its weakest link. Attackers do not need to breach well-protected areas of your system; they just need to identify the weakest point in your system and launch an attack through that point to complete the entire process. In the case of Bybit, the entire attack process goes as follows: it may first identify that this is a targeted attack because it has found that the Bybit SAFE wallet, the smart contract wallet, holds a significant amount of assets. Its target is the developer of this SAFE wallet because, as mentioned earlier, regardless of who performs the operation, it must be done through the UI provided by SAFE, which is the website used to operate your assets.
If I could breach the developer's computer through social engineering or other means and have the developer deploy malicious code on the SAFE website, then when anyone goes to the SAFE website to operate their wallet, the actions they see on the website would differ from the actual actions taking place on the blockchain. However, regular users would not be aware of this discrepancy. For example, just as a regular user operating within a bank's app might see a $100 transfer, whereas $900 is actually being transferred out, but the user is unaware because they see a $100 transfer within the app. If you breach the app's developer or the SAFE wallet's developer, making the actions shown in the wallet's UI different from the actual on-chain transaction rules, you can complete the entire attack process. This is essentially how the attack is carried out.
How can they obtain this developer permission? It is through some social engineering attacks, ultimately completing the entire attack process. Within this context, even when the SAFE developer is breached, there are still other opportunities. For example, if the wallet's signature can inform you of what transaction you are signing, and it differs from what you see on the website, there is still an opportunity. In the past, many banks had devices like U shields. If you have experience with them, you will notice that there is a display screen when you press a button on the U shield, which shows you that you are transferring $500 and asks for your confirmation. This device actually solves this problem because even if my app is attacked and informs me that I am transferring $100, the U shield will tell you that you are transferring $500 when you confirm, and you will notice the inconsistency.
Speaking of this specific Bybit case, if the wallet you signed with had a better alert capability, it could actually prevent such attacks. However, it is regrettable that in this case, even the hardware wallet used for signing did not perform particularly well. After the SAFE's UI was compromised, a malicious upgrade transaction was signed, allowing the attacker to take over the wallet and transfer $1.5 billion. So, this is a quite memorable incident.
This incident brings us a lesson that when dealing with a large amount of funds, you must perform cross-validation. You cannot trust a single provider or a single source of information. If you rely on a single provider or interface for information, as soon as that is compromised, the system link is broken. Therefore, you must perform cross-validation and have a third party verify from their perspective whether what you see is true. In such situations, you can further reduce the risk.
Firsthand Experience of Social Engineering Attack
Alex: In the case you just mentioned, there is a term called 'social engineering attack,' which not all listeners may understand the meaning of. Could you explain it?
Zhou Yajin: A social engineering attack, in full, is social engineering attack, which does not rely on technical means but rather on your work habits, interpersonal relationships, the job responsibilities you undertake, etc., targeting you with a set of attack methods tailored to you. I can give an example of a firsthand social engineering attack case that I experienced, which may help everyone understand better. As the CEO of BlockSeo, I often receive certain types of information, mainly in two categories. The first category is invitations to participate in podcasts, conferences, interviews, etc. The second category is from some investment institutions reaching out to discuss investment opportunities. I once encountered a situation where someone emailed me through our company email claiming to be from a certain investment institution, hoping to discuss investment opportunities.
Our security sense is relatively strong, and we would observe their email and domain. Sometimes we would conduct some background checks, looking at their company's website and investment portfolio. After checking, I found that this appeared to be a quite reputable institution, although I had never heard of them. So, I scheduled a meeting with him on the calendar. However, at this point, you would notice the first strange thing happening. When scheduling a meeting on the calendar, he did not provide any meeting link to me.
Usually, when scheduling a meeting, we would use services like Zoom, Google Meet, or other meeting software. But he did not provide any meeting link, just a time. When it was time for the meeting, I emailed him saying we are about to start the meeting and asked him to send me the meeting link. He immediately sent a meeting link, and when you click on this link, you will find something odd – he requires you to download a software.
If you lack experience at this point and feel anxious about an upcoming meeting, the attacker takes advantage of your anxious state by continuously urging you via email, bombarding you with emails. Eager to seize this opportunity, you may install the software without hesitation, only to find out later that it is a malicious video conference containing malware that steals the private keys stored on your computer. This is a social engineering attack that I have personally experienced. Therefore, you can see that the attacker targets my position in the company and the job responsibilities I hold, exploiting my pre-meeting anxiety to launch the attack.
Alex: I also saw a highly publicized incident in the industry a few days ago where the founder of a protocol claimed that while attending an offline event, their phone was left unattended for about fifteen minutes, and hundreds of thousands of funds from the phone's wallet were stolen. If this attack occurred while their phone was unattended, would this also be considered a form of social engineering attack?
Zhou Yajin: Yes, I think it is a form of social engineering attack, but it does not exactly fit our usual definition of a social engineering attack. Because in this case, his phone was only briefly unattended, and while someone may have approached him with the intention to take his phone, the process of unlocking the phone and accessing the funds inside requires significant technical expertise.
Security Principles When Interacting with Blockchain Protocols
Alex: Understood. We've just discussed some notable security incidents, so returning to the topic of ordinary individuals interacting with blockchain protocols, as you previously mentioned, many of the projects you have worked on are DeFi protocols, and many of us interact with DeFi protocols on the blockchain.
When interacting with these DeFi protocols or other protocols, are there any security principles that need to be followed? I believe that the majority of ordinary users do not have the ability to read code, and may even lack the ability to read signature information. In this situation, how can we minimize this risk as much as possible?
Zhou Yajin: I think if ordinary users are going to transact on the blockchain, they should first conduct some due diligence on the project team, which I think is quite important. When investing in an on-chain project, if you have a small investment amount and are testing the waters, that may be fine. However, if you are a serious investor looking to invest in a blockchain protocol with a significant amount of funds, you may need to conduct thorough due diligence on the project team. Due diligence in this context can be divided into several levels.
The first level is to say who the founder of the project is, whether they are anonymous, because some on-chain protocols are anonymous projects. You need to know the quality of this protocol, you need to know who the founder who is public-facing outside is, whether he has a history of rug pulling, this is very important. That is to say, you first need to do some background check on the composition of the protocol itself and the identity of the founder.
The second point is that you need to do some background check on the technical capabilities of the project team itself. You can see if this project has been audited by a top security company. Like you just mentioned, many users may not understand the technology, the code, may not understand the audit report, but you can download the audit report and simply review some key points. For example, which auditors, what is their reputation, are there any core security vulnerabilities in the report. It does not mean that if core security vulnerabilities are found in the report, the protocol is insecure. It actually means that the security company may be more diligent, it has found some security vulnerabilities, which will reduce the overall security risk of the project team, so you need to look at this matter dialectically. After conducting background checks on the project team, basically when you interact, you should also adopt a progressive approach, do not enter with a large fund volume at once, as the risk is still relatively high.
Another thing is that you need to rely on some professional security tools, such as some attack monitoring, some tools and platforms. If your fund volume is relatively large, you must always be aware of the security risks of the protocols you have invested in. You can monitor the overall security of the protocol you have invested in through platforms such as our Phalcon platform. For users with relatively small fund volumes, I think when conducting on-chain transactions, the main focus should be on preventing phishing risks. After all, the probability of a protocol being attacked is relatively low, but on-chain phishing, authorization, and other risks are indeed common risks that ordinary users may encounter on the chain.
To prevent these risks, it is best not to be too greedy, as there is no such thing as a free lunch. When you interact, try to confirm that it is an official website, not a counterfeit website. As for how to confirm that it is an official website, you may still need to have a certain ability to collect and organize information. Of course, you can also use some security tools to identify phishing websites. By doing this, you can avoid some risks.
Alex: I noticed an event, a few days ago Binance delisted the tokens of many projects, saying that they were unable to provide the operational aspects, so Binance delisted them. Then the project team said that due to various reasons, this project will no longer be operated, it is in a semi-abandoned state.
So, suppose a user used a DeFi protocol one or two years ago, and now the project team is not managing it, and the upgrade permissions for the code are not known. In cases like this specific scenario, could it be that because their upgrade permissions have not been properly managed, it may allow hackers or malicious actors to take control, and if your previous authorization has not been revoked, the funds in your wallet could be threatened by these subsequent impacts.
Yajin Zhou: Yes, this is also possible. Especially as you just mentioned, if a user authorizes their funds to some protocols, and these protocols and smart contracts may no longer be maintained in the future, if this authorization is not revoked, there is actually a security risk. The solution to this issue is that we always recommend ordinary users to regularly review their authorizations. You can revoke those authorizations that are not being used.
Many users may not fully understand which projects they have authorized, so we have created a tool called the Authorization Diagnosis Tool. You input an address, and we can tell you which protocols this address has authorized. We found that many users have authorized dozens of protocols, many of which are now inactive. These inactive protocols that have not received security upgrades may have security vulnerabilities. As long as there is a security vulnerability, someone can exploit that vulnerability in the protocol you have authorized to drain your funds, which is actually a significant risk.
Alex: Understood. I have another question about interaction security. In the past, we have seen that some attacked DeFi protocols or other protocols were relatively fewer in DEXs compared to lending or staking protocols. Is this related to the smart contract types of these two protocol categories, or are there other reasons?
Yajin Zhou: You are absolutely right. In relative terms, the security risk of DEX is lower than that of other protocols such as lending, yield farming, and some financial derivatives protocols. Firstly, the overall DEX protocol is relatively simple. The on-chain DEX protocol is basically the constant product (xy=k) formula. Of course, Uniswap V3 is slightly different, but the core principle is the constant product formula. Firstly, the protocol is simple, and secondly, it has a very good reference example, Uniswap. Many DEXs are forked from Uniswap, so by making some simple modifications, a DEX can be deployed. The overall security risk position of DEX is relatively lower.
However, for lending, yield farming, or other protocols that involve leverage, as well as protocols with more complex functionalities, the design of their protocols is inherently more complicated. For example, when creating a lending platform, the principle may sound simple, like depositing Asset A and borrowing Asset B, as long as you control the overall health of the assets everything is fine. But when it comes to supporting collateral assets, asset price fluctuations, and maintaining leverage support while ensuring the health of the user's funds even after repayment, the complexity of the protocol increases. This higher protocol complexity increases the probability of these protocols being attacked. I think this is the first reason.
The second reason is that a DEX itself does not hold funds. Of course, the funds inside a DEX are provided by liquidity providers, who are the ones providing liquidity. When a person actually uses the DEX, they just need to swap their token A for token B, and immediately token B comes back. Therefore, your assets are not inside the DEX's Pool. Even if the DEX's Pool is attacked, most users will not suffer losses; the losses will be borne by those providing liquidity. However, in lending platforms and other platforms, it is different because your assets are actually held there, and you are overcollateralized. In some other more complex protocols, there will inherently be a lot of users' assets held inside, so if it is attacked, the group of affected users will be quite large, which I think is the second reason.
Furthermore, we have also found that DEXs have actually been attacked in history. The reasons for their attacks are relatively simple. Firstly, the risk exposure of DEXs lies in authorization because when you swap, you need to authorize your own tokens to the DEX's router contract. Although the router contract does not hold funds, if there are any arbitrary execution vulnerabilities in the router contract, it could potentially siphon off all funds authorized to the DEX's users. We have found that most of the significant losses caused by vulnerabilities in DEXs are of this type, but this type is relatively easy to discover. As long as a qualified auditor is involved, it can actually be quite easy to detect.
Alex: So in the case of the authorization vulnerability you just mentioned, if an audit firm discovers such arbitrary execution permissions in a DEX, they generally advise against it, or they will alert everyone to this issue in the disclosure report?
周亚金: Yes, this is definitely a vulnerability and is certainly unreasonable. If a security company audits it, they must fix this, as it is a very critical vulnerability.
The Current State and Potential of the Blockchain Security Industry
Alex: OK, so we have just discussed many specific issues related to security attacks and defenses, as well as how to protect personal asset security. Let's now discuss the last question today, which is about the status of the blockchain security industry.
As you mentioned, in 2021 and 2022, due to the rise of DeFi, the blockchain security industry saw a significant increase in the number of clients. So, up to now, what is the approximate scale of the security industry, and what is its current status and profitability level?
Zhou Yajin: This is a very good question because in the blockchain security industry, you always need to know where the industry is currently at, where the ceiling is, in order to better develop your company. Currently, there is actually no recognized data on the total market cap of the entire blockchain security industry. However, there are some online reports or their own estimates suggesting that the overall size of the blockchain security industry is approximately around $30 billion per year. This scale is actually relatively small compared to the traditional cybersecurity industry. For example, by 2024, the entire traditional cybersecurity industry is expected to be around $1 trillion. Comparing $1 trillion to $30 billion, the gap is still quite large.
I think this is related to the current state of industry development because blockchain security essentially serves as a secure product and service for the blockchain industry, which is still relatively early stage overall. For example, a time period in the past that saw good development was during the DeFi Summer when some new innovative points emerged.
In the last year or two, after the DeFi Summer financial innovation craze passed, it seems that there hasn't been any particularly good and innovative new things coming in, resulting in the actual scale of the entire blockchain industry reaching its peak in 2022. I remember that at the time, the highest level of the entire blockchain security TVL should have been 177 billion, which is over $100 billion. But today, before I came on this show, I checked the data and the current TVL is 99 billion, which means it's a little over half of the peak, indicating that our blockchain industry seems to have encountered a bottleneck.
However, at the same time, we have also discovered the new potential of this industry, which is that traditional financial institutions are slowly entering this industry. The entry of traditional financial institutions into the industry has some signals, such as traditional banks issuing stablecoins on-chain that are regulatory compliant. Traditional payment processors like Stripe supporting crypto payments. Some are cross-border payments using crypto to solve the payment issues faced by traditional cross-border e-commerce.
So we will find that although there hasn't been the kind of innovation brought by DeFi Summer in '21 and '22 that drove TVL to new highs, traditional financial institutions and merchants with real-world demand are entering this industry, and after they enter, they will bring about the industry's standardization. For an industry to develop on a large scale, it must develop compliantly within a regulatory framework and system. I think this is the opportunity we can see in the past year or two. So overall, the overall size of the blockchain security industry is still relatively small and in its early stages. But with the entry of traditional financial institutions and more and more standardization after compliance, I think there is still great potential for explosive growth here; this is my own observation.
Moat of Top Security Companies
Alex: Got it. I am very impressed. Around 2021 and 2022, it felt like security companies in the blockchain space, especially those doing smart contract audits, were making a lot of money. Some well-known security companies even made you feel privileged if they could squeeze in your audit quickly. What do you think are the main moats of those top security companies?
Zhou Yajin: I think there might be a few points. The first point is about branding and trust. Especially in security audits, it is a service that requires a very strong brand recognition. As you mentioned earlier, when the market was doing well, audits were in high demand, and there could be long wait times. In fact, today, top security audit companies still face such a situation, meaning that a project cannot immediately receive auditing resources upon request. The top security companies with a strong brand effect are still in a state of high demand and low supply. So, I think one moat is branding and trust, how to establish a good brand image in the blockchain security industry, and the trust that comes behind the brand, whether it comes from users, projects, or other participants, which is very important.
The second point is the need for security innovation technology. Apart from addressing blockchain security issues and conducting security audits, are there really no other supplemental solutions needed? Security audit can only solve the security issues before the smart contract is deployed on the chain, by conducting a security review. However, after the project is launched, the project team may adjust parameters, make daily configurations, or perform routine upgrades without further audits due to queuing or cost considerations, resulting in security issues in smart contracts deployed for various reasons. We cannot rely solely on security audits to solve such problems. There needs to be some security innovative technology and products to address such issues. This is also what distinguishes BlockSec from other blockchain security work. Apart from providing security audit services for smart contract security before protocol launch, we also have a platform for monitoring and blocking attacks after the smart contract goes live. This is the only blockchain security company globally that combines smart auditing and attack monitoring, covering the entire smart contract lifecycle. This is very important, that is, you need security innovation technology and products to help users truly solve problems in this market.
The third point is compliance, regulation, and geopolitical influences. The crypto industry will definitely need to operate under compliance and regulation to have the opportunity for mass-scale development. Not everyone agrees with this view, but having spent many years in this industry, we can see that the industry must develop under sunlight and comply with regulatory frameworks to attract traditional funds into this industry. In this context, being proactive in developing compliant products and services is essential. Compliance and regulatory product services require a deep understanding of the industry's regulatory policies and compliance requirements, which can then be productized. In addition, the so-called geopolitical influence is when some regions consider geopolitical factors when choosing suppliers. For example, regulatory bodies in Hong Kong may be more inclined to select non-U.S. suppliers' products. So, when you have a deep understanding of regulatory policies and compliance, good products, and some geopolitical influence, I believe this is the moat of a blockchain security company.
Alex: Got it. Today we discussed the topic of crypto security from various angles, from a specific security incident to some security principles that everyone should pay attention to, and also including the overall development scale of the industry, and so on. Thank you very much, Zhou Yajin, for joining our show today to share these insights. I hope we can have another opportunity in the future to discuss more related topics.
Zhou Yajin: Thank you, Alex.
Disclaimer: The content of this article solely reflects the author's opinion and does not represent the platform in any capacity. This article is not intended to serve as a reference for making investment decisions.
You may also like
Honda prepares to send its hydrogen tech to space
Share link:In this post: Honda is working with Sierra Space and Tec-Masters, two space technology companies, to try their high-differential pressure water electrolysis system. Honda aims for hydrogen to help it get all of its cars off carbon by 2040. Honda says it will work with NASA to get the equipment to the ISS on Sierra Space’s Dream Chaser space plane.
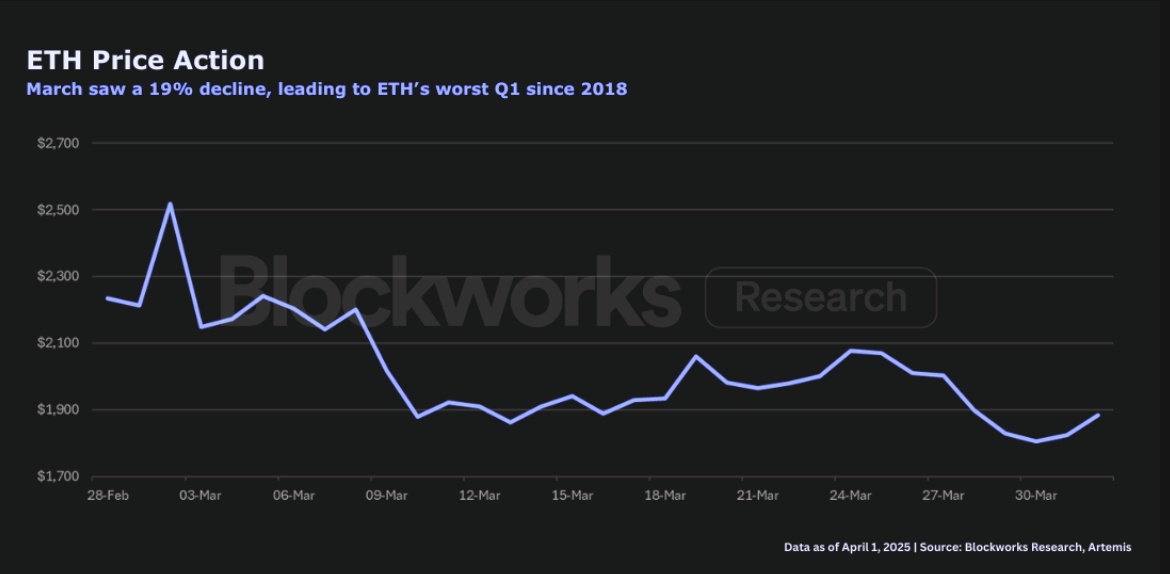
ETH just had lowest quarterly return since Q2 2022: Blockworks Research
The network is at a “pivotal juncture,” Blockworks Research’s Marc-Thomas Arjoon said
Riot Platforms Hits Post-Halving Bitcoin Production High as It Expands AI Capacity
Solana Price Pattern Points to a 65% Surge as Key Metric Beats Ethereum by Far
